If there’s one universal truth in cybersecurity right now, it’s that identity is the new perimeter. Firewalls and VPNs still have their place, but in a world where everyone’s hybrid, everything’s in the cloud, and AI tools are plugged into every workflow, managing identity and access is the real game.
That’s where Identity and Access Management (IAM) comes in. Think of IAM as your company’s VIP list—making sure only the right people (and devices) get in, and only to the right areas. In 2025, getting IAM right isn’t optional—it’s critical.
In this guide, we’ll explore IAM best practices in 2025, share actionable steps to tighten your security, and connect it to your broader Zero Trust Security strategy. Let’s get into it.
Why IAM Matters More Than Ever in 2025
The digital identity explosion is real. With remote work, cloud ecosystems, and third-party integrations multiplying by the day, every new account is a potential attack vector. Cybercriminals aren’t just hacking networks anymore—they’re hacking people through stolen credentials, social engineering, and privilege escalation.
IAM is your defense mechanism against all that chaos. Done right, it not only prevents breaches but also boosts compliance, improves user experience, and saves your IT team countless headaches.
1. Adopt a Zero Trust Model (and Stop Handing Out Blind Trust)
The first rule of modern IAM? Don’t trust anyone by default. That’s the essence of Zero Trust Security—the idea that every request, whether from inside or outside your network, must be verified continuously.
A Zero Trust approach to IAM includes:
- Continuous authentication and authorization
- Network segmentation to isolate sensitive resources
- Real-time risk-based access controls
If you want to dive deeper into how Zero Trust fits into your overall architecture, check out our detailed guide, Zero Trust Security: A Practical Implementation Roadmap.
2. Make Multi-Factor Authentication (MFA) Phishing-Resistant
Passwords are like umbrellas in hurricanes—barely helpful. Multi-Factor Authentication (MFA) is non-negotiable, but not all MFA is equal.
Avoid outdated methods like SMS codes or push notifications, which are vulnerable to phishing and SIM-swapping attacks. Instead, use phishing-resistant MFA such as:
- FIDO2 hardware tokens
- Biometric authentication (fingerprint or facial recognition)
- PKI smartcards tied to verified devices
The goal? Create authentication methods that hackers can’t trick with fake login pages or intercept via social engineering.
3. Follow the Principle of Least Privilege (PoLP)
The fewer permissions people have, the smaller your attack surface. The Principle of Least Privilege (PoLP) ensures every user or service account only has the minimum access needed to do their job.
Regularly review and revoke outdated permissions to avoid privilege creep, where users accumulate unnecessary access over time. Use just-in-time (JIT) access for sensitive systems—grant permissions only when needed and automatically expire them afterward.
4. Automate Provisioning and Deprovisioning
Manual onboarding and offboarding are an identity disaster waiting to happen. Automation ensures no one slips through the cracks.
Modern IAM systems let you:
- Automatically create and revoke accounts when employees join or leave
- Sync roles across HR and IT systems
- Enforce policy-based access controls
Not only does this reduce human error, but it also slashes the time it takes to respond to potential insider threats.
5. Centralize Identity Governance and Federation
In 2025, most organizations run a mix of cloud, hybrid, and on-prem systems. Without centralized control, it’s easy to lose visibility.
Centralized Identity Governance and Administration (IGA) helps you manage access policies, monitor compliance, and streamline audits. Combine that with federated identity and Single Sign-On (SSO) to give users a frictionless experience while maintaining full oversight.
If your IAM setup feels like juggling chainsaws blindfolded, centralization is your safety net.
6. Review and Audit Access Regularly
Access reviews aren’t fun—but they’re essential. Set up quarterly audits (or better yet, continuous monitoring) to catch:
- Dormant or orphaned accounts
- Privilege escalations
- Policy violations
Integrate IAM with Security Information and Event Management (SIEM) platforms for proactive detection of anomalies. That way, when an intern suddenly tries to log into your cloud root account, you’ll know.
7. Protect Admins with Privileged Access Management (PAM)
Privileged accounts are prime hacker bait. Treat them with the paranoia they deserve.
A solid Privileged Access Management (PAM) program includes:
- Mandatory MFA for all admin accounts
- Session monitoring and recording
- Credential rotation after each use
- Just-in-time (JIT) access provisioning
With PAM in place, even if an attacker compromises one admin account, they can’t roam freely or maintain persistence.
8. Go Passwordless – Because Passwords Are Garbage
We’ve all been there—forgotten passwords, endless resets, sticky notes on monitors. Passwords are not just inconvenient—they’re a security liability.
Enter passwordless authentication:
- Biometrics (fingerprint, facial ID)
- Passkeys linked to devices
- WebAuthn standards for browser-based security
Not only does passwordless authentication improve security, but it also reduces user friction—a rare win-win in cybersecurity.
9. Establish Governance and Compliance Frameworks
IAM without governance is chaos with a login screen. Clearly define who owns your IAM policies, how access is managed, and how compliance is verified.
Tie everything to regulations relevant to your business—GDPR, HIPAA, SOX, or industry-specific standards—and perform regular compliance checks. Documentation isn’t glamorous, but it’ll save your company when auditors come knocking.
10. Train Your People – They’re Still Your First Line of Defense
You can have the best IAM tech on the planet, but if your users reuse passwords or click phishing links, it’s game over.
Run regular security awareness training that focuses on:
- Phishing and social engineering recognition
- Credential best practices
- Reporting suspicious behavior
Empower users to be part of the security culture instead of its weakest link.
11. Choose IAM Tools That Scale and Integrate Seamlessly
Scalability is the unsung hero of good IAM design. Choose platforms that can grow with your business and integrate with your existing HR, cloud, and IT service management (ITSM) systems.
The goal is to avoid “security silos” that make life harder for both IT and end users. A unified, API-driven IAM solution ensures smooth operations and consistent policies across your environment.
12. Keep Improving – Security Never Sleeps
Cyber threats evolve daily. Your IAM strategy should too.
Schedule annual risk assessments, penetration tests, and red team simulations to evaluate how resilient your IAM setup really is. Feed those results back into your governance framework to keep improving over time.
IAM isn’t a project—it’s a process.
The 2025 IAM Landscape: What’s Next?
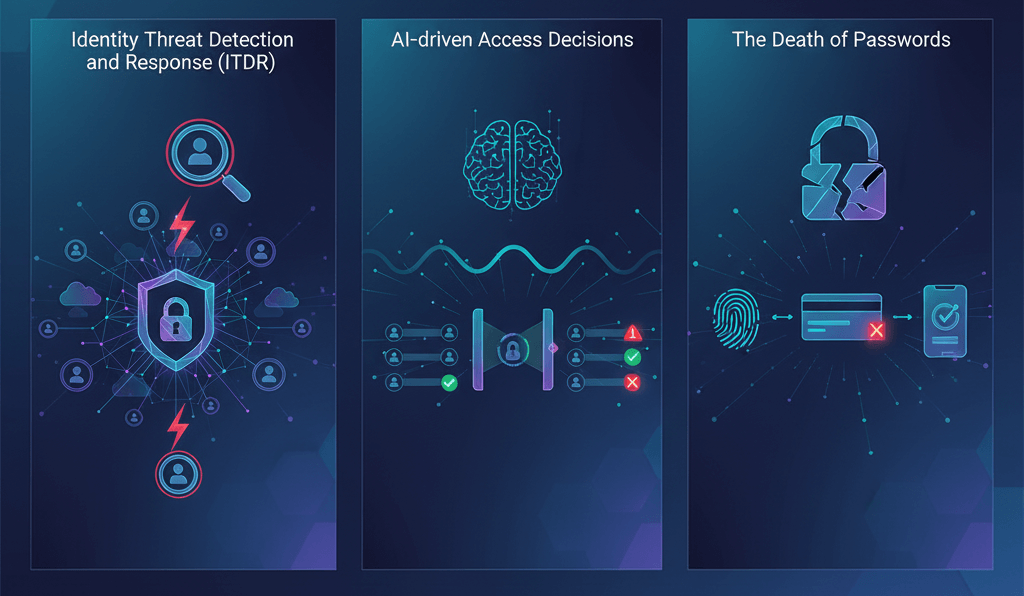
A few trends defining the IAM space this year:
- Identity Threat Detection and Response (ITDR): The fusion of IAM and threat analytics for faster detection.
- AI-driven Access Decisions: Machine learning models flag unusual login behaviors and adjust risk dynamically.
- The Death of Passwords: Passkeys, biometrics, and smartcards are the new normal.
The future of IAM isn’t just about access—it’s about adaptive trust powered by data and automation.
IAM Implementation Roadmap
Here’s how to bring all these best practices together:
- Assess: Evaluate your current IAM maturity and gaps.
- Define: Set clear goals aligned with compliance and business outcomes.
- Engage: Bring in stakeholders from IT, HR, and compliance.
- Pilot: Start small—test your IAM approach on critical systems.
- Automate: Connect your IAM tools to existing workflows.
- Train and Review: Educate users and audit continuously.
Simple, strategic, and sustainable.
The Bottom Line
In 2025, IAM is your organization’s digital backbone. It protects your users, secures your systems, and supports your entire cybersecurity framework.
By following these best practices—adopting Zero Trust, enforcing MFA, embracing passwordless, and continuously auditing—you’ll build a resilient, scalable, and future-proof IAM program.
And remember, strong identity security isn’t about locking everything down—it’s about trusting intelligently.