Zero Trust Security: A Practical Implementation Roadmap
Zero Trust has evolved from a security buzzword to a fundamental cybersecurity framework that organizations worldwide are adopting to address modern threats. Operating on the principle of “never trust, always verify,” Zero Trust eliminates implicit trust from network architectures and requires continuous validation of every user, device, and transaction. This comprehensive roadmap provides actionable guidance for organizations embarking on their Zero Trust journey.
Understanding Zero Trust Architecture
Zero Trust Architecture (ZTA) represents a paradigm shift from traditional perimeter-based security models. Rather than assuming everything inside the network is trustworthy, Zero Trust treats all access requests as potentially hostile, regardless of origin. The architecture comprises three core logical components working together to enforce security policies:
Policy Engine makes real-time access decisions by evaluating identity, device health, location, behavioral patterns, and threat intelligence before granting or denying access to resources.
Policy Administrator translates the Policy Engine’s decisions into actionable commands, establishing or terminating connections between subjects and resources.
Policy Enforcement Points act as gatekeepers that enable, monitor, and terminate connections between users and enterprise resources, communicating continuously with the Policy Administrator.
Core Principles and Tenets
The NIST SP 800-207 framework establishes seven fundamental tenets that guide Zero Trust implementation:
- All data sources and computing services are considered resources, extending Zero Trust practices to all devices and applications
- All communication is secured regardless of network location, eliminating the concept of a trusted internal network
- Access to individual resources is granted on a per-session basis, evaluating trust before granting least-privilege access
- Access is determined by dynamic policy, incorporating behavioral and environmental attributes alongside identity verification
- The enterprise monitors and measures asset integrity continuously, patching systems and tracking security posture
- Resource authentication and authorization are dynamic and strictly enforced, implementing IAM policies with MFA before allowing access
- The enterprise collects comprehensive information about assets, infrastructure, and communications to continuously improve security posture
The Five Pillars of Zero Trust Maturity
The CISA Zero Trust Maturity Model organizes implementation around five interconnected pillars:
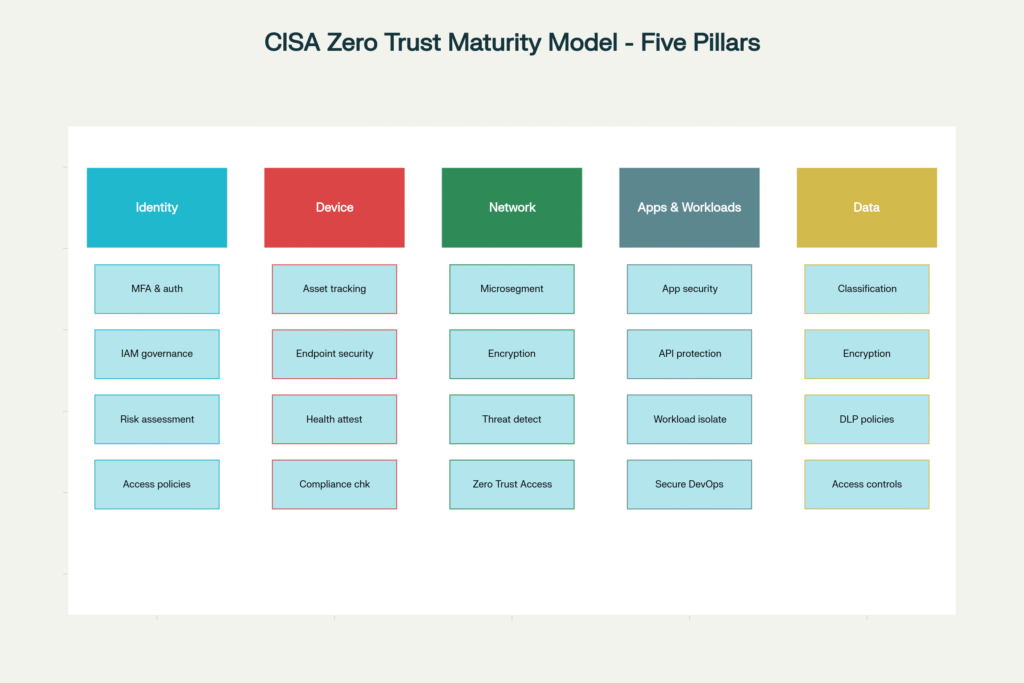
These pillars work together to create a comprehensive security framework. Identity serves as the foundation, establishing who or what is requesting access. Device ensures that endpoints meet security requirements. Network implements microsegmentation and encrypted communications. Applications and Workloads secure the software layer, while Data protects information regardless of location.
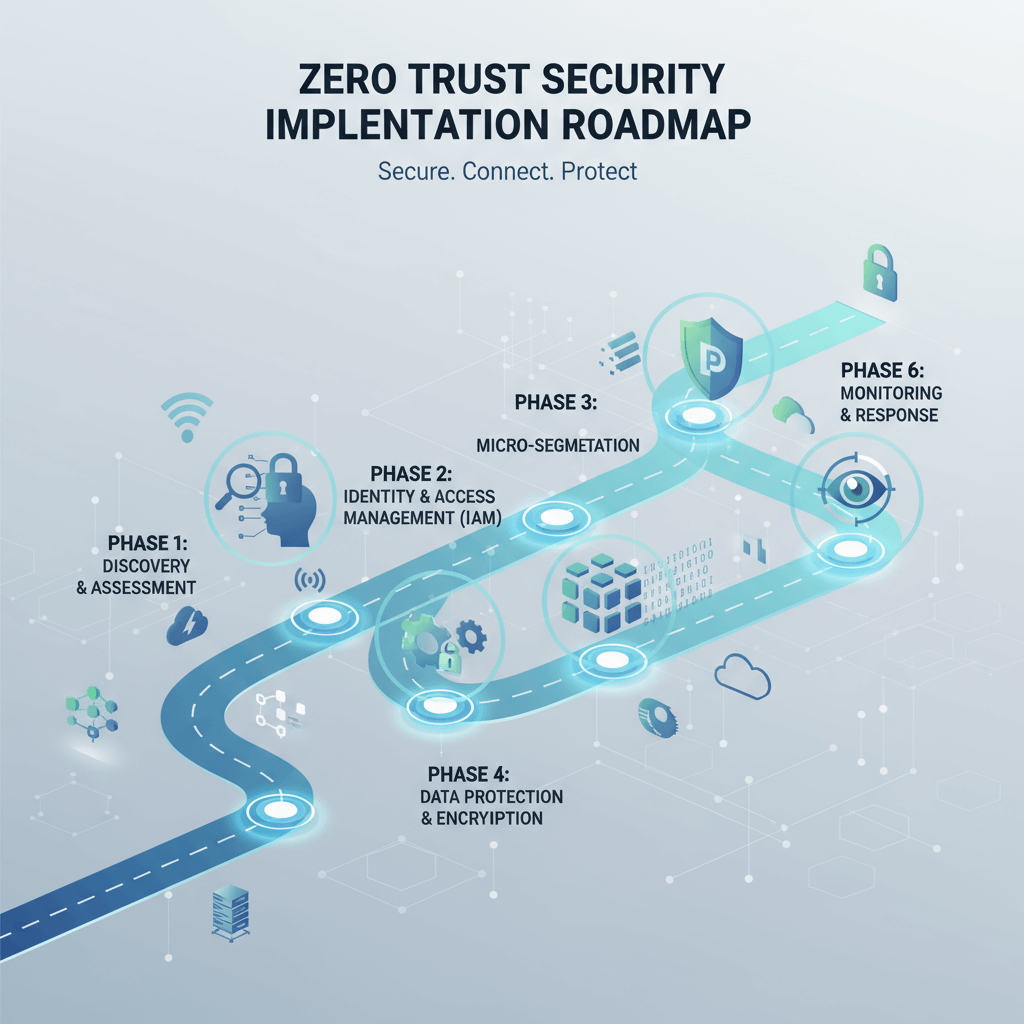
Phased Implementation Approach
Successful Zero Trust adoption requires a structured, phased approach that delivers incremental value while managing organizational change:
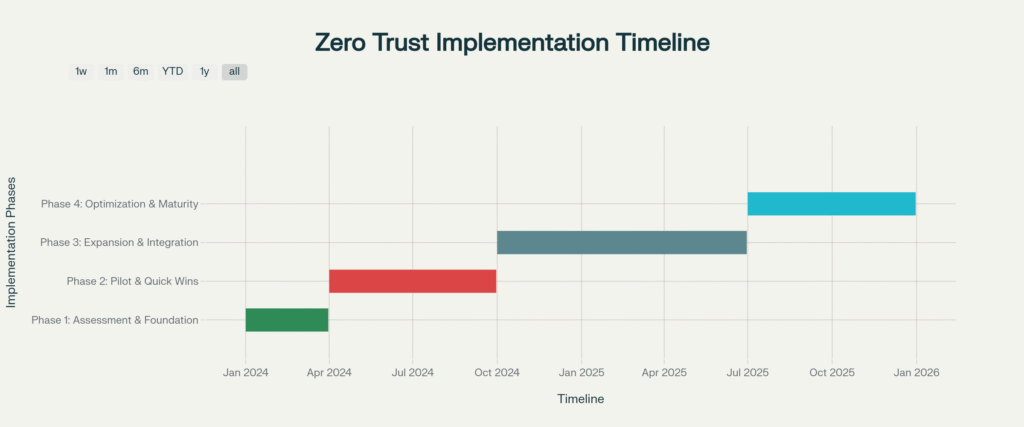
Phase 1: Assessment and Foundation Building (Months 1-3)
Begin by establishing comprehensive understanding of your current security posture:
Conduct Security Posture Assessment: Evaluate existing security infrastructure, policies, and controls to identify vulnerabilities and gaps. Document current authentication methods, access controls, network segmentation, and monitoring capabilities.
Identify and Classify Critical Assets: Determine which Data, Applications, Assets, and Services (DAAS) are essential to business operations. Prioritize based on sensitivity, business criticality, and potential impact if compromised. Develop a data classification framework with clear sensitivity levels.
Map Data Flows and Transaction Patterns: Document how data moves between systems, users, and applications. Analyze network traffic to understand normal operational behaviors and identify dependencies influencing segmentation decisions.
Define Protect Surface: Focus on defining a minimal “protect surface” containing only critical DAAS elements. This concentrated approach makes security controls more manageable and effective.
Secure Executive Sponsorship: Develop a compelling business case demonstrating Zero Trust ROI through risk reduction, operational efficiency, compliance benefits, and productivity enhancements. Present the strategy as enterprise-wide security transformation with active C-level sponsorship.
Phase 2: Pilot and Initial Implementation (Months 4-9)
Focus on achieving quick wins that demonstrate value while building organizational confidence:
Strengthen Identity and Access Management: Implement robust IAM as the cornerstone of Zero Trust:
- Deploy cloud-based identity management integrating on-premises directory services
- Roll out MFA across all user accounts, prioritizing privileged access
- Implement Single Sign-On (SSO) to consolidate authentication
- Establish role-based and attribute-based access control policies
- Block legacy authentication protocols
Implement Device Trust and Endpoint Security: Establish comprehensive device security before granting network access:
- Deploy endpoint detection and response (EDR) solutions
- Implement Mobile Device Management (MDM) or Unified Endpoint Management (UEM) platforms
- Require device health attestation including OS updates, encryption status, and security software presence
- Issue device certificates for cryptographic identity binding
Deploy Initial Microsegmentation: Begin network segmentation to limit lateral movement:
- Identify critical systems requiring isolation
- Implement software-defined networking or next-generation firewalls
- Create security zones around high-value assets
- Define and enforce inter-segment communication policies
Start with High-Impact, Low-Complexity Projects: Target 10-15 most-used applications for initial Zero Trust controls. Focus on cloud-based applications where implementation is simpler and benefits are immediately visible.
Phase 3: Expansion and Integration (Months 10-18)
Scale Zero Trust controls across the organization while deepening integration:
Implement Zero Trust Network Access (ZTNA): Replace traditional VPNs with identity-based, per-application access. Deploy ZTNA solutions verifying user identity, device health, and contextual signals before granting access. Applications remain invisible to unauthorized users, reducing exposure.
Deploy Data Protection Controls: Implement comprehensive data security aligned with classification:
- Apply sensitivity labels based on classification framework
- Implement Data Loss Prevention (DLP) policies
- Deploy encryption for data at rest and in transit
- Establish rights management controlling access and sharing
Establish Continuous Monitoring and Analytics: Deploy SIEM and behavioral analytics:
- Aggregate logs from all Zero Trust components
- Implement User and Entity Behavior Analytics (UEBA)
- Configure real-time alerting for policy violations
- Integrate threat intelligence feeds
Secure Applications and Workloads: Extend Zero Trust to application layer and cloud workloads:
- Implement application-aware firewalls and API gateways
- Deploy workload protection platforms securing containers and VMs
- Enforce least-privilege access at the application level
- Establish runtime application self-protection (RASP)
Expand Microsegmentation: Increase network segmentation coverage targeting 95%+ of workloads. Apply granular policies governing east-west traffic using identity-aware segmentation rather than IP-based rules.
Phase 4: Optimization and Maturity (Months 19-24+)
Achieve advanced Zero Trust maturity through automation, optimization, and cultural integration:
Automate Policy Enforcement: Leverage automation and orchestration platforms:
- Implement Security Orchestration, Automation, and Response (SOAR) platforms
- Automate provisioning and de-provisioning workflows reducing manual processes by 80%
- Deploy automated threat response capabilities
- Use AI/ML for dynamic policy adjustments
Implement Advanced Analytics and AI: Deploy sophisticated threat detection and response:
- Utilize machine learning models for predictive threat detection
- Implement behavioral biometrics for continuous authentication
- Deploy deception technologies integrated with Zero Trust controls
Foster Security Culture: Embed Zero Trust principles in organizational culture:
- Conduct comprehensive security awareness training programs
- Implement simulated phishing campaigns
- Deploy Human Detection and Response (HDR) technologies
- Establish security champions program in each business unit
Key Implementation Strategies
Start with Identity: Identity serves as the control plane for Zero Trust, making IAM the logical starting point. Strong identity verification ensures only authenticated entities access resources. Implement MFA universally and integrate all applications with your identity provider.
Prioritize Based on Risk: Focus initial efforts on protecting crown jewel assets—the systems and data most critical to business operations or most attractive to attackers. This risk-based prioritization ensures maximum security impact.
Think in Segments, Not Perimeters: Abandon perimeter thinking in favor of microsegmentation. Divide the network into small, isolated zones with granular controls between them, preventing lateral movement and limiting breach impact.
Embrace Least Privilege Access: Grant users and services only minimum access necessary to perform specific functions. Implement just-in-time (JIT) and just-enough-access (JEA) principles where elevated privileges are granted temporarily, then automatically revoked.
Verify Device Health Continuously: Before granting access, verify devices meet security requirements including current patches, active endpoint protection, enabled encryption, and compliance with configuration policies.
Technology Stack and Solutions
A comprehensive Zero Trust implementation typically involves multiple integrated technologies:
Identity and Access Management: Microsoft Entra ID, Okta, JumpCloud, Ping Identity
Zero Trust Network Access: Cloudflare One, Zscaler Private Access, Palo Alto Prisma Access, Twingate
Endpoint Protection: CrowdStrike Falcon, Microsoft Defender, SentinelOne, Carbon Black
Microsegmentation: Illumio, Zero Networks, VMware NSX, Cisco Tetration
SIEM and Analytics: Splunk, Microsoft Sentinel, IBM QRadar, Elastic Security
Data Protection: Microsoft Purview, Symantec DLP, Digital Guardian, Varonis
Cloud Security: Zscaler, Netskope, Palo Alto Prisma Cloud, AccuKnox
Measuring Success and ROI
Establish comprehensive metrics to demonstrate Zero Trust value and guide continuous improvement:
Organizations with mature Zero Trust implementations achieve significant business outcomes: 246% ROI over three years, \$1.76 million average savings per breach, 80% reduction in provisioning time, and 40-60% reduction in audit preparation time.
Common Challenges and Solutions
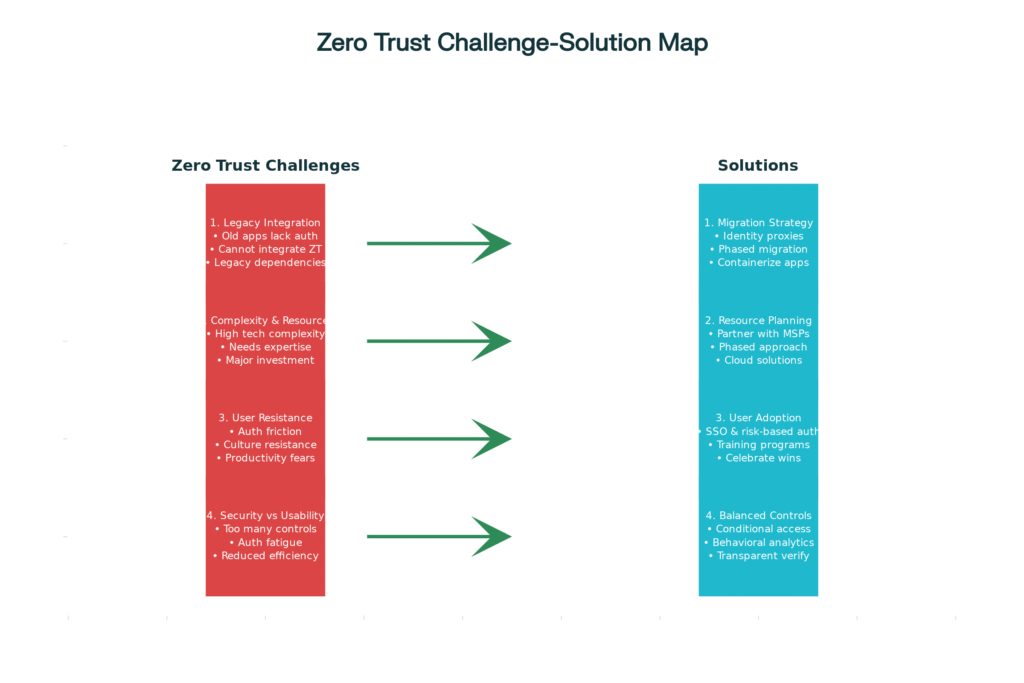
Legacy System Integration: Legacy applications often lack support for modern authentication. Implement Zero Trust incrementally, prioritizing modern applications while using identity proxies, application delivery controllers, or containerization to extend Zero Trust controls to legacy infrastructure.
Complexity and Resource Constraints: Zero Trust involves significant technical complexity and resource investments. Partner with experienced security vendors or managed service providers. Adopt a phased approach spreading costs over time. Leverage automation to reduce operational overhead.
Cultural Resistance and User Experience: Employees may resist continuous verification and additional authentication steps. Invest in comprehensive change management and security awareness training. Design user experiences minimizing friction through SSO, risk-based authentication, and context-aware policies.
Balancing Security and Usability: Excessive controls can frustrate users and hamper productivity. Implement risk-based conditional access that adjusts security requirements dynamically. Use continuous authentication and behavioral analytics to verify users transparently.
Governance, Risk, and Compliance Integration
Zero Trust naturally supports regulatory compliance and governance frameworks. Zero Trust principles align with requirements from GDPR, HIPAA, PCI DSS, SOC 2, and NIST frameworks. Strict access controls, encryption, continuous monitoring, and detailed audit trails directly address most compliance mandates.
Organizations can automate compliance verification through policy engines that enforce regulatory requirements in real-time. Comprehensive logging and monitoring provide detailed audit trails demonstrating compliance, with organizations reporting 40-60% reduction in audit preparation time.
Building Executive Support and Business Case
Securing and maintaining executive sponsorship is critical to Zero Trust success:
Align with Business Objectives: Frame Zero Trust as a business enabler supporting digital transformation, remote work capabilities, cloud adoption, and customer trust. Demonstrate how security improvements enable rather than constrain business initiatives.
Quantify ROI: Build comprehensive business cases including avoided breach costs, operational efficiency gains, compliance cost reductions, and productivity improvements. Use industry benchmarks and peer comparisons to contextualize potential benefits.
Demonstrate Progressive Value: Achieve visible quick wins demonstrating tangible benefits within 3-6 months. Use these successes to build confidence for broader implementation phases.
Provide Executive Education: Invest in structured security education for leadership addressing both conceptual understanding and practical implications. Use threat briefings, peer benchmarking, and scenario-based learning to build executive fluency.
The Path Forward
Zero Trust represents not a destination but a continuous journey toward improved security maturity. Organizations should view their implementation roadmap as iterative, regularly reassessing priorities, incorporating lessons learned, and adapting to evolving threats and business needs.
Success requires balancing technical implementation with cultural transformation. While technologies provide capabilities, people and processes determine whether those capabilities translate into effective security outcomes. Organizations that invest equally in technology, training, and change management achieve significantly higher Zero Trust maturity.
Start with a thorough assessment, secure executive sponsorship, focus on quick wins, and build momentum through incremental successes. With persistence, appropriate resources, and commitment to “never trust, always verify,” organizations can transform their security posture and build resilient defenses protecting critical assets in an increasingly hostile digital environment.
1 thought on “Zero Trust Security: A Practical Implementation Roadmap”
Comments are closed.